PROTECTION OF DISKS OR FILES WITH THE SET COMMAND

THE SET COMMAND
SET is one of the most neglected utilities that has a whole series of useful, entertaining and interesting functions to offer. It is the utility that all people concerned about the security of their files should know about; you can hide them and protect them with passwords. you can even put passwords on disks.
Security is an often overlooked aspect of computing. It affects many important factors, so you should think carefully about what you want when talking about it. The most obvious goal of security is to prevent others from getting their hands or eyes into our own data.
SET has no absolute solution to this problem except possibly for extremely simple users. In the end, the only way to protect your data from prying eyes is to keep the drive it's stored on under lock and key.
Much more important from a practical point of view is the security of the data, in the sense of protecting it against accidental (or intentional) loss or damage. It is in this area where SET can play a good role.
To learn more about SET and how to use it, first grab a disk to experiment with. In it should be stored the files SET.COM, INITDIR.COM, TYPE.COM, ERASE.COM, DIR.COM, SHOW.COM and a nice variety of weird files to play with (including some simple ASCII ones). Once you've done that, it's time to initialize the drive for all other operations, so type INITDIR A: or B: if you're using a second drive. We will now assume that the unit is A.
After initializing the disk we can try the first trick, giving it a name. Type:
- SET ¡NAME=HARRIEY¿
Of course, it can be anything you want. Giving the drive a name can be fun, but it lacks functionality. In fact it's hard to think of its possible use, especially if you can only read with LABEL.
SECURITY FILES
We'll quickly skip to the most useful thing, we're going to set all the files on the disk to Read Only; this will allow you to use the COM files (the actual programs), and read the following files. This prevents a deletion of the files. So now type:
- SET A:*.* ¡RO¿
This sets up an attribute bit that tells the system not to allow any alteration of the file. It basically prevents files from being deleted or written to with CP/M but does not hide them in any way; a DIR would expose them.
Putting *.* in the command means that all files on disk are affected by the commands. It is clear that it is faster to specify them all together than to name them individually. But what if you decide you need to alter or delete one of the files? The response is to return to the Read Write state with the following statement:
- SET FILENAME.TYP ¡RW¿
Obviously it will replace FILENAME.TYP with the actual name of the file. Preparing your application software for Read Only is very effective in preventing it from being erased. Once prepared, not even the ERA *.* command will be able to delete it. So now you know how to avoid accidental deletion of your files; however, people can still read their text files or run COMs. How can you avoid it?
One possibility is to set your files in the System state. It's what most software companies did. The little Mini Office, for example, contains a bunch of System files, as well as the LocoScript disks (yes, even LocoScript works on a modified version of CP/M).
BUCKING (OPPOSITION OF CIRCUITS) OF THE SYSTEM
System files have some strange properties. As far as CP/M is concerned, the most important thing is that a Group 0 System file can be accessed from any group. This is not very important on floppy disk systems since few CP/M users work with other groups, but on hard drives it can be very useful. You can keep all your applications in Group 0 and work in less confusing groups dedicated to particular activities - Group 1 for database work, Group 2 for word processing, and so on.
The other important capability of a filesystem is that it doesn't even show a DIR listing; all it gets is “System file(s) exist” but it doesn't say much else. You can prepare a file as Read Only and System with the command:
- SET FILENAME.TYO ¡RO SYS¿
Read Only and System can be set to any file without running INITDIR first, making them very suitable for everyday use. If you know the name of the file, you can run it (if it's a COM file) or type it (TYPE, if it's a text file) with the normal commands; the only thing that happens is that you can see them listed when you do a DIR. It also gives the file enormous protection, but is there anything else you could do?
Of course yes; you can set a password for your files. This is one of the operations you can only do on a disk prepared with INITDIR. They are two processes; you have to enable disk password protection first and then make it effective. Use the commands:
- SET ¡[PROTECT ON¿
- SET A:*.TYP ¡PASSWORD=BEANO¿
You can use any of the wildcard commands for files, so the password can be put on one file, on all of the same type (as above), or on all files on disk using *.*. This is one of those things where you need some sensitivity; a single password for all files makes more sense than a different one for each, after all, it can be nice to try searching all files in case you forget the magic word.
HOW TO PROTECT
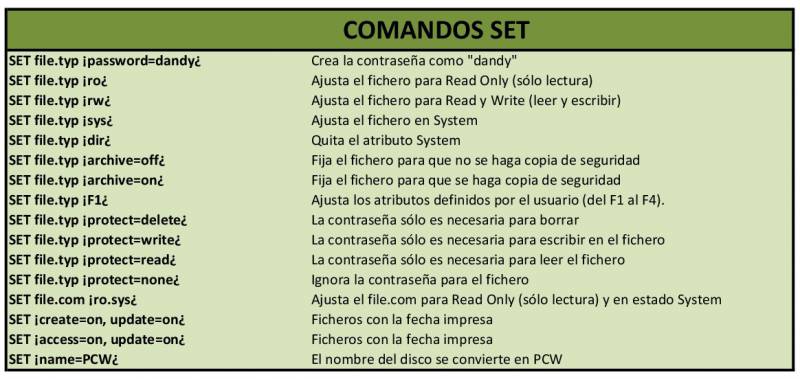
There are quite a few parameters of the SET command. Below we leave you with a complete list of them and the functions they perform. File.typ is the name to be replaced with the name of the file of interest or a wildcard file specification.
PRINTING THE TIME
One of the most notable things that SET offers is the printing of the date of the files. These can carry their date and time of creation and last update. It is not possible to have all three. To display them you need DIR.COM. You just have to type:
- DIR ¡date¿
The only problem with printing dates is that you need to initialize PCW with the date and time (using the DATE utility) every time you start working with PCW so that everything stays in order. If you are going to need this facility frequently, you should seriously consider a built-in clock (such as the one that SCA Systems puts in their Centronic interface). With a simple SUBMIT file you can set the correct date and time every time you turn on your PCW.
TECHNICAL BIT
What exactly does SET do? Each character in the PCW is maintained as an eight-bit binary number, but only the first seven are needed to define it. The eighth is normally a zero but can be used as an indicator. The three characters of the file type can each have their own set of bits, and each means something different to CP/M.
Likewise, the first four characters can have their bit set for use by the CP/M user or programmer. Since the CP/M stores spaces in file names, even if you don't type anything it can set the file type bits even if none are used.
MAKE BACKUP COPIES
Perhaps even more important than preventing other people from accessing your files is making sure that you always have them yourself.
For some reason, probably because storing data on disk seems more like magic than technology, PCW users tend to have too much faith in the reliability of disks. Although it is true that they were much more reliable before than now due to the passage of time, a quick look in any manual on CP/M will reveal an appalling number of utilities to get rid of old disk sectors.
Trust the disks if you don't have anything stored on them. A corollary to Murphy's Law states that the disk will fail at the critical moment it is needed.
One way to ensure that you always have a backup of any altered files is to make use of a file's Archive attribute, which can be turned on and off using SET. What you have to do is set all the files to Archive on and then start refreshing them by setting only those files you want to backup to Archive off. Now when you use PIP to make a copy of your files, you only have to tell it to make a copy of all the files that have been altered using the Archive off parameter. The whole sequence is as follows:
- SET A:*.*¡ARCHIVE=ON¿
- SET A:*.DAT¡ARCHIVE=OFF¿
- PIP B:=A:*.*¡A¿
Now PIP will only copy files whose Archive attributes have been turned off. Use this technique for the first backup, and then set all file attributes back to “on”. With the pip command you will only be able to copy in the future the files you have altered (since altering a file also sets the Archive attribute to “off”).
Although this technique is simple, you need to work a lot with it to master it. Its worth doing. Setting up a system that automatically backs up at the end of the day could save you hours of work and rebuilding data files.
Warnings
There are one or two things to know about passwords: TYPE.COM and ERASE.COM seem to recognize them (there may be other commercial programs that do). When accessing a password-protected file, most programs simply display a BDOS error. Even CP/M doesn't ask for a password, it just indicates the error.
LocoScript reacts somewhat differently. It completely ignores passwords and happily copies, deletes or alters even protected files, so if you forget a password all you have to do is copy the file with LocoScript and the new version will be fully accessible.